Slides for this presentation are available to registered HCSS community members. Please log in to access the file.
Once logged in, you may download the slides here: [HCSS 2026 Amorim]
If you do not already have an account, you may create one here:
https://sos-vo.org/user/register
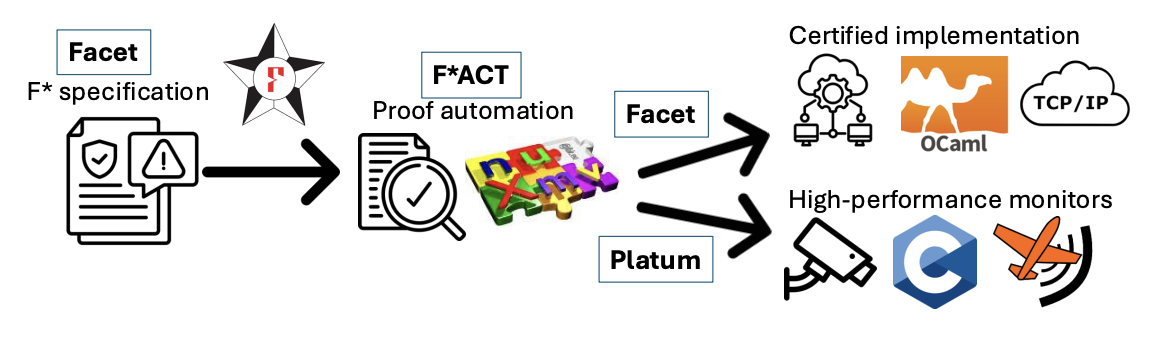
ABSTRACT Communication protocols govern every safety-critical cyber-physical system, yet the gap between a formally verified protocol model and the code that actually executes has remained an open problem [4,3]. Tools such as TLA+ [7] verify models in isolation, session type frameworks provide structural guarantees but cannot prove application-specific safety properties, and no prior work has mechanized the metatheory of Refined Multiparty Session Types (RMPSTs) [8,6], leaving correctness guarantees resting on hand-written proofs. Addressing the HCSS theme of Verifiable Automatic Code Generation, we present a unified F* framework that closes this gap: safety properties proved over a shared formal model extend to every artifact the framework synthesizes. The framework displayed in Figure 1 comprises three composing contributions. Facet provides the first mechanized RMPST metatheory, proving eight core theorems, including deadlock freedom, subject reduction, and runtime soundness, by construction for any protocol written in our DSL. F*ACT is a proof automation framework that connects protocol conformance to application specific physical safety: given a protocol specification and a system model with a distinguished Wrong state encoding unsafe configurations, F*ACT proves via bisimulation that no conforming execution trace reaches Wrong, using automated nuXmv model generation for finite-state protocols and Meta-F* tactics dispatching to Z3 for protocols with larger data domains. Platum synthesizes allocation-free C finite state machines directly from verified F* specifications, enabling deployment on resource-constrained hardware with 13.3 µs per-message overhead and no garbage collection. The composition theorem is the central result: because all three tools extract from the same RCFSM deep embedding over which safety is proved, verified implementations, distributed runtime monitors, and C proxy monitors for legacy systems all inherit the safety guarantee without independent re-verification. We demonstrate the framework on MAVLink and Modbus [1,2,5], two of the most widely deployed industrial protocols, showing that stealthy attacks – sequences of individually valid commands that drive a system into an unsafe state – are blocked at runtime.
Fig. 1: A single high-level specification feeds a safety proof framework and generates three verified artifacts: static OCaml implementations, distributed TCP/IP monitors, and C runtime monitors References
|
BIO Arthur Amorim is a Ph.D. candidate in Computer Science at the University of Central Florida, advised by Dr. Gary T. Leavens, with an expected graduation of July 2026. Since 2022, he has been a formal methods researcher at Idaho National Laboratory's National and Homeland Security Directorate, where he leads development of SPECTRE: a framework for specification, verification, and deployment of safe cyber-physical protocols utilizing the F* theorem prover. His research focuses on closing the gap between formally verified protocol models and deployed code, with applications to UAV systems (MAVLink/ArduPilot/PX4) and industrial control systems (Modbus). His work spans the full stack: RMPST metatheory mechanized in F*, system-specific safety proofs, and the extraction of high-assurance protocol implementations and runtime monitors. |